VLX BWC V1X PJ Mid Mount Backplate - bwc mounts
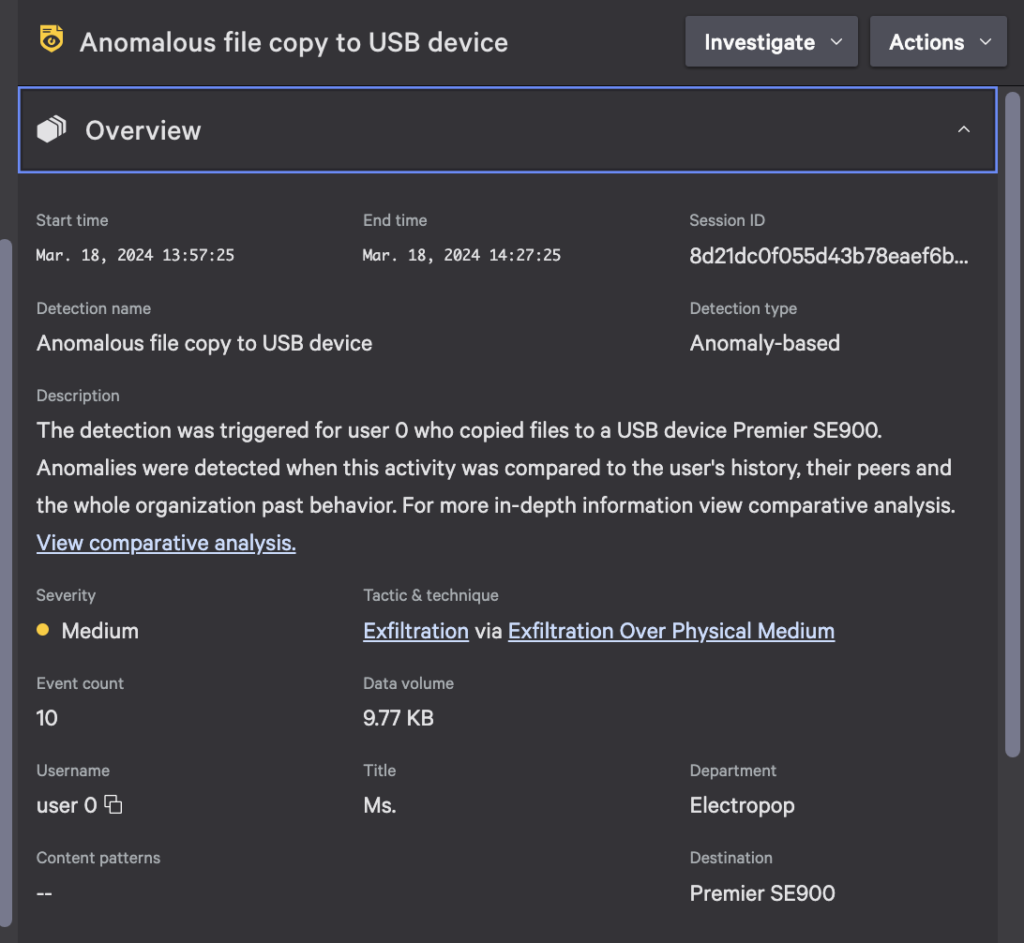
The threat of data exfiltration looms over organizations of all sizes. With the introduction of Falcon Data Protection Detections, organizations now have a powerful tool to effectively identify and mitigate data exfiltration risks. Below, we delve into examples of how Falcon Data Protection Detections can identify data exfiltration via USB drives and web uploads, highlighting the ability to surface threats and prioritize them for mitigation.
Time is of the essence when it comes to protecting your data, and often, teams are sifting through hundreds or thousands of alerts to try to pinpoint truly malicious user behavior. Manual triage and response takes up valuable resources, so machine learning can help busy teams prioritize what to tackle first and determine what warrants further investigation.
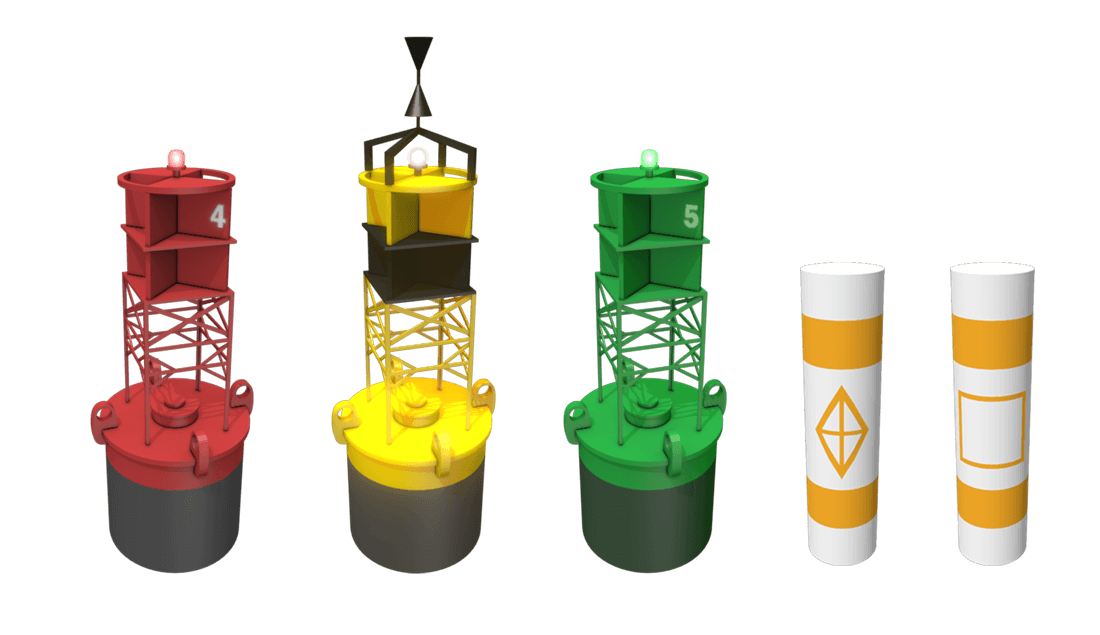
These are white with a blue horizontal band. They are usually placed in marinas and other areas where vessels are allowed to anchor. These are the only buoys you may legally tie up to.
201942 — "An inspiring tribute to female friendship and female courage!"--Kate Quinn, New York Times bestselling author of The Alice Network and The ...
In another scenario, a malicious insider may attempt to exfiltrate an unusual file type containing sensitive data by uploading it to a cloud storage service or file-sharing platform. By monitoring web upload activities and correlating them against a user’s typical file types egressed, Falcon Data Protection Detections can identify suspicious behavior indicative of unauthorized data exfiltration — even if traditional rules would have missed these events.
Flexibarrier -Expanding Barrier - with base (3m) Regular Price: £143.04 Discount Price £79.20 Exc. VAT £95.04 Inc. VAT View Details
Safe watermark characteristics
In both examples, Falcon Data Protection Detections demonstrates its ability to surface risks associated with data exfiltration and provide security teams with the insights they need to take swift and decisive action. By using advanced machine learning models and integrating seamlessly with the rest of the CrowdStrike Falcon® platform, Falcon Data Protection Detections empowers organizations to stay one step ahead of cyber threats and protect their most valuable asset — their data.
Combining the manual approach with the assistance of advanced machine learning models and automation brings the best of both worlds, paired with the institutional knowledge and subject matter expertise of your team.
Mooringmarker
When you integrate with Falcon Fusion SOAR, you can create workflows to precisely define the automated actions you want to perform in response to Falcon Data Protection Detections. For example, you can create a workflow that automatically generates a ServiceNow incident ticket or sends a Slack message when a high-severity data exfiltration attempt is detected.
For example, a disgruntled employee may connect a USB drive to transfer large volumes of sensitive data. Falcon Data Protection’s ML-based detections will identify when the number of files or file types moved deviates from that of a user’s or peer group’s typical behavior and will raise an alert, enabling security teams to investigate and mitigate the threat.
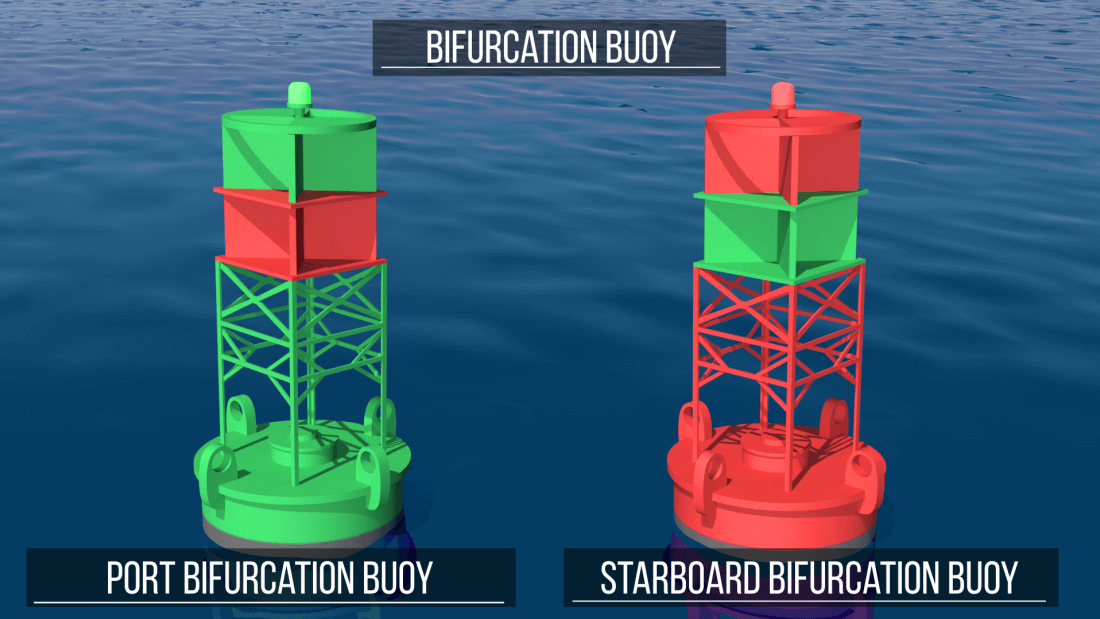
Junction markers indicate the preferred channel at points where the waterway splits or branches off in another direction.
Special mark buoy
Find many great new & used options and get the best deals for Sky Hero SPYDER 700 Multirotor Drone Kit at the best online prices at eBay!
Since ordinary dust masks are not effective in preventing the inhalation of asbestos fibres and dust, the selection of the appropriate respiratory solution is ...
Isolated danger mark
2022520 — As others have stated here, tasers are quite finnicky. If you want a less-lethal defensive item with firearm like ergonomics, the JPX Cobra is ...
Traditional approaches to data exfiltration detection often rely on manual monitoring, which is labor-intensive and time-consuming, and strict behavior definitions, which lack important context and are inherently limited in their effectiveness. These methods struggle to keep pace with the rapidly evolving threat landscape, making it challenging for organizations to detect and mitigate data exfiltration in real time. As a result, many organizations are left vulnerable to breaches. By pairing manual data classification with the detections framework, organizations’ institutional knowledge is enhanced by the power of the Falcon platform.
Safe watermarkers boating
Types of buoys & markers What does this non-lateral marker indicate? Regulatory and informational markers are easily identified through which features?
The new Detections capability in CrowdStrike Falcon® Data Protection reduces friction for teams working to protect their organizational data, from company secrets and intellectual property to sensitive personally identifiable information (PII) or payment card industry (PCI) data. These detections are designed to revolutionize the way organizations detect and mitigate data exfiltration risks, discover unknown threats and prioritize them based on advanced machine learning models.
In the ever-evolving landscape of cybersecurity threats, organizations must continually innovate their detection methodologies to stay ahead of adversaries. Our approach leverages user behavioral analytics at three distinct levels — User Level, Peer Level and Company Level — to provide organizations with comprehensive protection and increase the accuracy of detections.
By aligning detection algorithms with the organization's unique business processes, security teams can more accurately identify deviations from expected activity and prioritize them based on their relevance to the organization's security posture. For example, anomalies that deviate from standard workflows or access patterns can be flagged for further investigation, while routine activities are filtered out to minimize noise. Additionally, behavioral analytics at the Company Level enable organizations to adapt to changes in their environment such as organizational restructuring, new business initiatives or shifts in employee behavior. This agility ensures detection capabilities remain relevant and effective over time.
Rigid Alpha Flag is flown by a vessel engaged in diving operations. This flag does not substitute for the diver-down flag above in states that require the diver-down flag. You will usually see both flags in use. The alpha flag indicates that the vessel is restricted in ability to maneuver, in this case due to the nature of its work.
Safe waterMark lights
Directional / Leading Tactile Indicators. The minimum set-back requirement for Directional Tactiles is also 300mm from any hazard / obstacle. The intent is to ' ...
At the Company Level, user behavioral analytics are magnified to account for the nuances of each organization's business processes and to tailor anomalies to their expected activity. This involves incorporating domain-specific knowledge and contextual understanding of the organization's workflows and operations based on file movements and general data movement.
The Details panel includes the detection’s number of files and data volume moved versus the established baselines per user, peers and the organization. This panel also contains contextual factors such as first-time use of a USB device or web destination, and metadata associated with the file activity, to better understand the legitimate reasons behind certain user behaviors. This nuanced approach provides a greater level of confidence that a detection indicates a true positive for data exfiltration.
Found only on the Mississippi River and its tributaries as defined by the U.S. Coast Guard in Rule 3 of the COLREGs. These aids to navigation are not numbered as in IALA-B system. Numbers indicate mileage from a fixed point. Lights on green aids show a single-flash which may be green or white. Lights on red aids show a group-flash which may be red or white. Diamond-shaped crossing dayboards, red or green as appropriate, are used to indicate where the river channel crosses one bank to the other.
2023410 — Warning Sign "VERY SHARP (270 DEGREE) CURVE AHEAD (W1-15), Warning Sign "SHARP CURVE TO RIGHT (W1-8)" is shown as, Warning Sign "INTERSECTION ...
It is with deep sadness that we announce the passing of Lynda Buchanan, a cherished volunteer of the Grand Prairie Police Department. Lynda, along with her ...
Safe water Markerbuoy
On bodies of water wholly within state boundaries and not navigable to the sea, each state is responsible for establishing and maintaining aids to navigation. A uniform system of aids and regulatory markers has been agreed to by all states.
Divers’ Flag indicates that scuba divers or snorkelers are operating in the area. Stay well clear of this flag. Many states have specific distance-away requirements from 100 to 300 feet. Check your state regulations.
Falcon Data Protection Detections uses advanced machine learning algorithms and behavioral analytics to identify anomalous patterns indicative of data exfiltration. By continuously monitoring user behavior and endpoint activities, Falcon Data Protection can detect and mitigate threats in real time, reducing the risk of data breaches and minimizing the impact on organizations' operations. Automation enables organizations to scale their response capabilities efficiently, allowing them to adapt to evolving threats and protect their sensitive assets. With automated investigation and response, security teams can shift their efforts away from sifting through vast amounts of data manually to investigating and mitigating high-priority threats.
Safe water markercolor
At the User Level, behavioral analytics are employed to understand and contextualize each individual user's benchmark activity against their own personal history. By analyzing factors such as file activity, access patterns and destination usage, organizations can establish a baseline of normal behavior for each user.
Behavioral analytics can also be applied at the Peer Level to identify cohorts of users who exhibit similar behavior patterns, regardless of their specific work functions. This approach involves clustering users based on their behavioral attributes and analyzing their collective activities. By extrapolating and analyzing user cohorts, organizations can uncover anomalies that may not be apparent at the User Level.
Using machine learning algorithms, anomalies that deviate from this baseline are flagged as potential indicators of data exfiltration attempts.
Detect, prevent, and respond to attacks— even malware-free intrusions—at any stage, with next-generation endpoint protection.
Be alert and prepared to stop. As you approach a crossing - whether marked or uncontrolled - remember to slow down and look both ways. You must stop if you see ...
Open the PDF file with data you must censor. · Select the Security tab from the main ribbon. · Click "Mark Redaction." · Select the text you wish to redact, which ...
For example, if an employee and their peers typically only handle office documents, but one day the employee begins to upload source code files to the web, a detection will be created even if the volume of activity is low, because it is so atypical for this peer group. This approach surfaces high-impact events that might otherwise be missed by manual triage or rules based on static attributes.
Detect, prevent, and respond to attacks— even malware-free intrusions—at any stage, with next-generation endpoint protection.
In addition to the aforementioned anomaly detections, you can configure rule-based detections associated with your data classifications. This enhances the power of data classification to assign severity, manage triage and investigation, and trigger automated workflows. Pairing these with anomaly detections gives your team more clarity into what to pursue first and lets you establish blocking policies for actions that should not occur.



 Ms.Cici
Ms.Cici 
 8618319014500
8618319014500